Our Security Services & Solutions Built to Protect.
From penetration testing to 24/7 SOC monitoring — we deliver the full spectrum of cybersecurity capabilities that modern enterprises demand, all under one roof.
Complete Security Coverage — Every Layer
From red team engagements to compliance consulting — every service built on certified expertise and real-world threat intelligence.
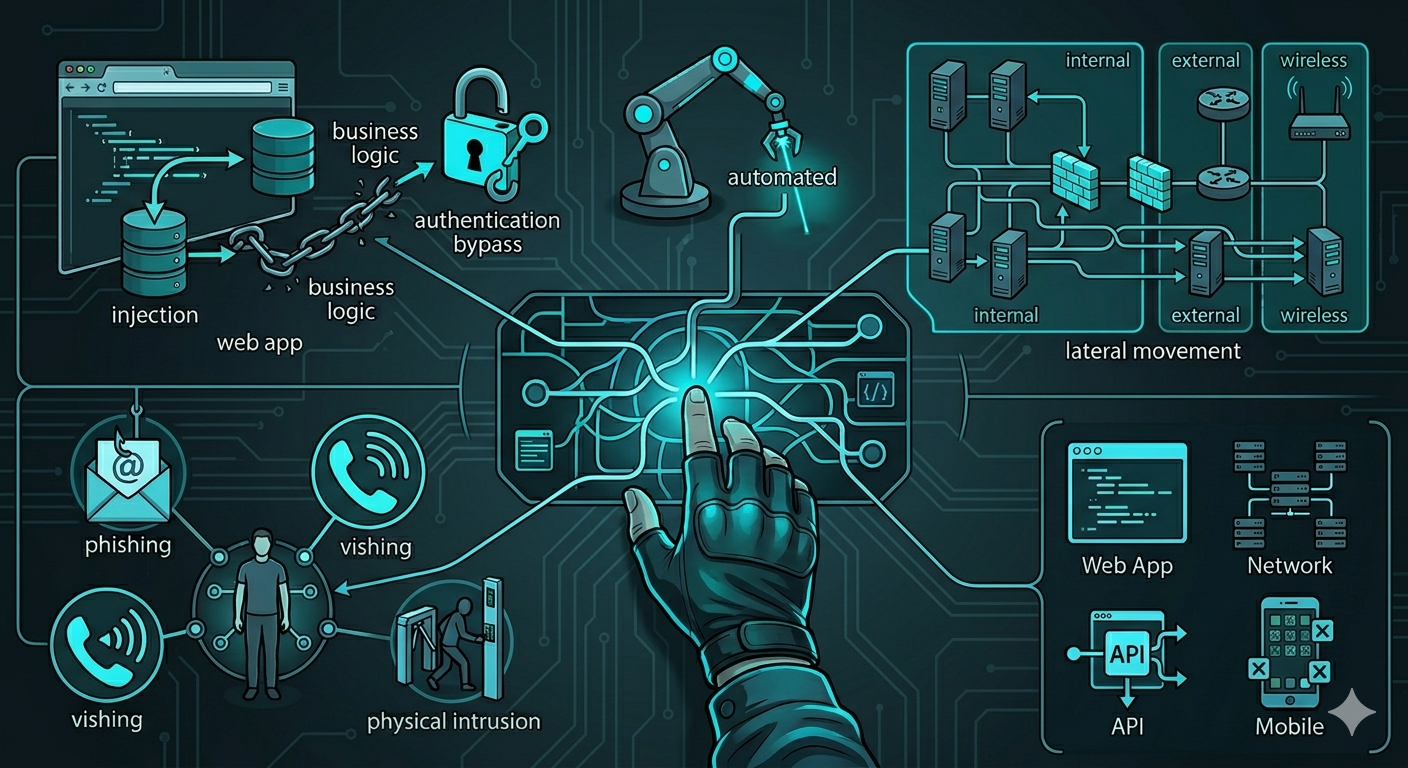
Attack Your Systems Before They Do
Our OSCP-certified ethical hackers simulate real-world attacks using the same tools and persistence as advanced threat actors — surfacing what automated scanners miss.

Your 24/7 Cyber Shield
Our SOC never sleeps. AI-augmented analysts monitor your full environment in real time, detecting and neutralising threats before they escalate — backed by a contractual SLA.

Hunt Hidden Threats Inside Your Network
Already breached? Our forensic team hunts for indicators of compromise, lateral movement, data exfiltration, and persistence mechanisms lurking silently in your environment.

Transform Your Team Into Human Firewalls
Phishing simulations, tailored eLearning modules, and executive briefings that measurably reduce risk — because your people are your most critical security control.
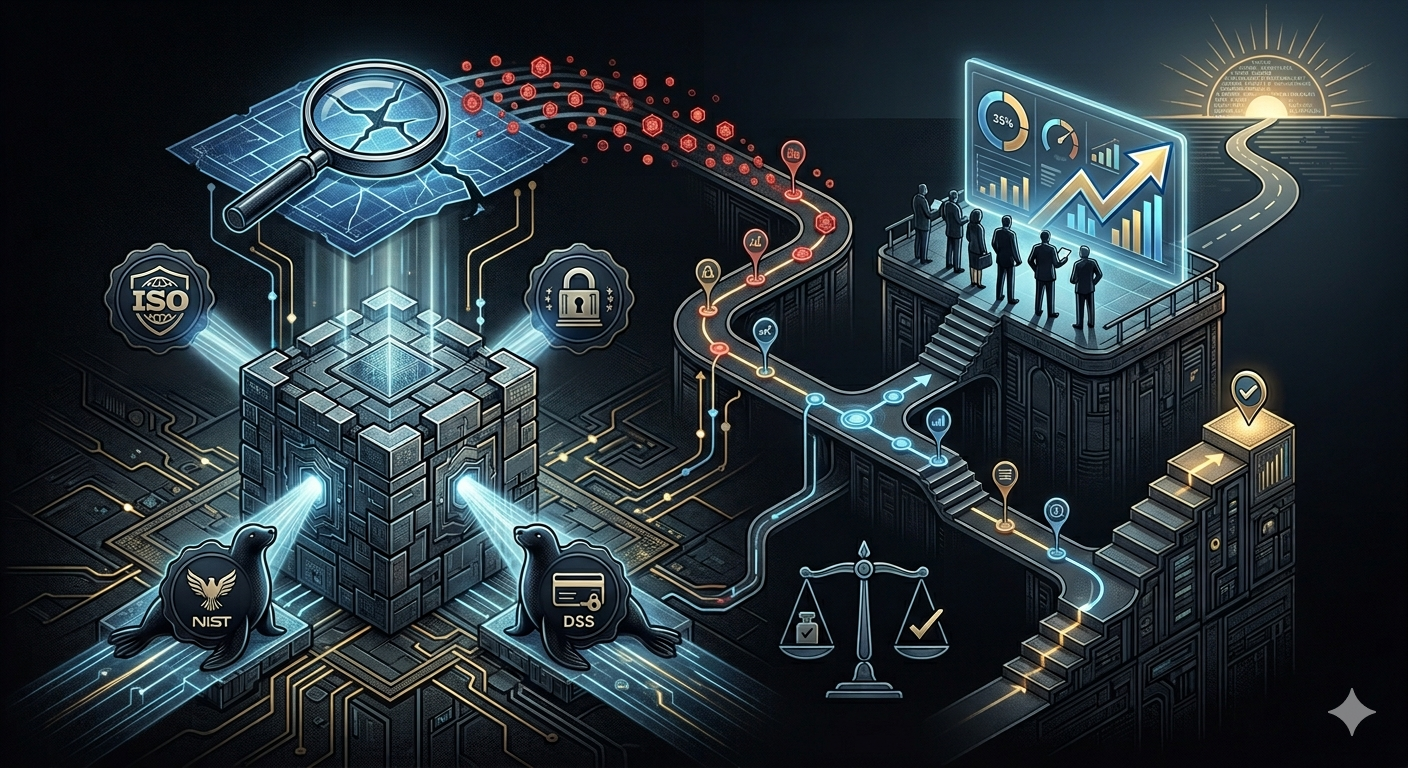
Close Every Gap Before Auditors Do
Comprehensive IS audits against ISO 27001, SOC 2, NIST, and local regulations — with gap analysis, prioritised roadmaps, and board-ready reporting that simplifies your compliance journey.

Build Resilient Governance From the Ground Up
We design and implement GRC programs that align your security posture with business objectives and regulatory requirements — across every industry vertical, at every maturity level.
Expanded Security Capabilities
Specialist offerings built for the most demanding environments — from cloud infrastructure to industrial control systems.

Secure Every Cloud Configuration
AWS, Azure & GCP security assessments, misconfiguration detection, CSPM, and identity posture management — keeping your cloud environment locked down across every dimension.

Test Your Defences Under Real Threat Conditions
Full-scope adversary simulation across physical, digital, and social vectors — testing whether your detection, response, and resilience hold up against a motivated, persistent attacker.

Secure Your App Before Launch
Static and dynamic analysis of iOS and Android applications against OWASP Mobile Top 10 and platform security guidelines — ensuring your mobile products can be trusted by users and regulators alike.

Turn Privacy Into a Competitive Advantage
GDPR, PDPA, and sector-specific privacy compliance programmes with DPO-as-a-service and data mapping — helping your organisation build lasting customer trust through responsible data stewardship.

Custom Web Application Development
End-to-end design and engineering for secure, scalable web applications — from discovery and UX to APIs, deployment, and hardening aligned with OWASP and your compliance needs.
Our Engagement Process
A structured, transparent methodology that delivers value from day one and keeps you informed every step of the way.
Discovery & Scoping
We work with your team to define objectives, boundaries, and success criteria for the engagement — no surprises.
Assessment & Testing
Our certified analysts execute the engagement using industry-leading tools, TTPs, and proprietary methodologies.
Reporting & Briefing
Detailed technical report plus an executive summary — with prioritised findings, evidence, and clear remediation steps.
Remediation & Retest
We support your team through fixes and conduct a complimentary retest to verify all critical findings are resolved.
Don't Wait for
a Breach to Act
Get a free, no-obligation security assessment from our certified experts. We'll map your full exposure in 48 hours — before attackers do.